Endpoint Protection Management is a crucial aspect of cybersecurity strategy
Endpoint Protection Management is a crucial aspect of Muttii Group’s cybersecurity strategy. They utilize leading solutions like Symantec Endpoint Protection Manager, Microsoft Endpoint Protection, and Sophos Central Endpoint Protection to safeguard their endpoints from malware, viruses, and unauthorized access. The centralized management platforms, such as SEPM Symantec and Symantec Endpoint Manager, enable efficient oversight of endpoint security. Complementing these are tools like Endpoint Security Manager and Microsoft Defender SCCM.

Muttii Cyber Protect Cloud with Endpoint Protection Management
Announcement
Muttii is partnering with Noname Security to deliver advanced API security capabilities.
Benefits
The email security services offered by Muttii Group provide numerous benefits to organizations and individuals

Comprehensive Security
Endpoint protection solutions offer a multi-layered defense against various cyber threats, safeguarding critical data and systems from malware, ransomware, and other malicious attacks.

Centralized Management
With centralized management platforms, such as Symantec Endpoint Protection Manager and Sophos Central Endpoint Protection, Muttii Group can efficiently manage and monitor security.

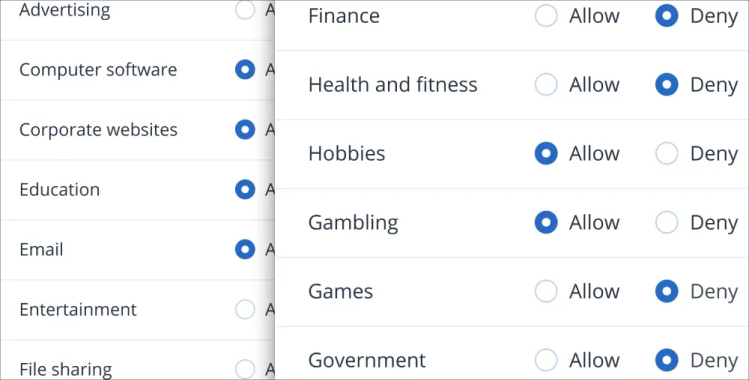
Real-time Insights
Endpoint protection tools provide real-time insights into the security posture of endpoints, allowing for proactive threat detection and rapid response to potential incidents.

Seamless Integration
Integration with other security and management tools, like Microsoft Defender SCCM and System Center Configuration Manager, streamlines security operations and enhances overall efficiency.

Improved Compliance
Endpoint protection management solutions aid Muttii Group in maintaining regulatory compliance, ensuring that industry-specific security standards and data protection regulations are met.

Disaster Recovery
Solutions like Symantec Endpoint Protection Manager offer disaster recovery capabilities, enabling swift restoration of systems and data in the event of an attack or system failure.
Features
Patch management
Software patches and updates are essential to securing a business environment and can fix known vulnerabilities before they become issues. With patch management support for Microsoft and third-party software on Windows, you can easily schedule or manually deploy patches to keep data safe.

Fail-safe patching
Skip the additional hardware and installation and set up your disaster recovery plan in three clicks. Choose between multiple templates with different configurations of recovery servers, enabling you to set up disaster recovery plans quickly and easily.
Remote desktop and assistance
Employees working from home may need access to files or apps on their work machines and they might not have a configured VPN. Share a secure link with end users so they can remotely access their machine.
Capabilities
Threat Prevention
Proactively identifying and blocking known and unknown threats, such as malware, viruses, ransomware, and zero-day attacks, through signature-based and behavior-based detection methods.
Incident Response
Facilitating rapid incident response by providing real-time alerts and comprehensive visibility into endpoint activities, enabling quick investigation and remediation.
Data Protection
Implementing data loss prevention measures, encryption, and access controls to safeguard sensitive data and prevent unauthorized access or data leakage.
Policy Enforcement
Enforcing security policies across all endpoints to maintain consistent security standards and ensure compliance with industry regulations.
Patch Management
Automatically updating software applications and operating systems with the latest security patches to address vulnerabilities and reduce the attack surface.
Web and Email Security
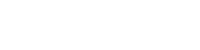
Scanning and filtering web and email content for malicious links, attachments, and phishing attempts to prevent users from falling victim to cyber threats.
Pricing
Sold on an annual basis
Case Studies
Learn how customers applied Muttii API Connect to improve their API Management strategies

Linten Technologies migrates to Cyber Protect Cloud to streamline
Muttii Cyber Protect Cloud is purpose-built for service providers and after doing its due

Central University of Technology Successfully Migrates from Legacy
The Central University of Technology (CUT) is a higher education institution

The Detroit Pistons and Centaris #TeamUp to support cyber protection
Federal Bank uses Muttii API Connect to offer top-tier banking

Cloudtech SAS switches to Muttii Protect Cloud from Arcserve to better support its customers
Cloudtech SAS (Cloudtech) is a Colombian systems integratorand managed services provider.

Diadem solves technical and commercial challenges by selecting Muttii Cyber Cloud
Diadem’s existing vendor provided an unacceptable level of service andsupport across many mission-critical dimensions.

Data Consult Grows Managed Cloud Services, Product Portfolio,
Data Consult recognized the importance of cloud computing and theneed to offer managed services to its customers.
Frequently Asked Questions
Endpoint Protection Management refers to the process of securing and managing endpoints, such as desktops, laptops, servers, and mobile devices, within an organization’s network. It involves deploying security measures, enforcing policies, and monitoring endpoint activities to protect against cyber threats and data breaches.
Endpoint Protection Management is crucial because endpoints are often the entry points for cyberattacks. By securing and managing endpoints, organizations can prevent malware infections, data leaks, and unauthorized access, ensuring data and system integrity.
Endpoint Protection Management employs various techniques to detect threats, including signature-based detection, behavior-based analysis, machine learning algorithms, and real-time threat intelligence feeds. These methods allow the system to identify known and unknown threats.
Yes, Endpoint Protection Management can prevent data loss through features like data loss prevention (DLP), encryption, access controls, and policy enforcement. These measures safeguard sensitive data and prevent unauthorized access or leakage.
Yes, modern Endpoint Protection Management solutions are designed to handle mobile devices as well. They offer Mobile Device Management (MDM) capabilities, securing and managing smartphones and tablets within the organization.
Endpoint Protection Management typically includes patch management functionality, automatically updating software applications and operating systems with the latest security patches to address vulnerabilities.